So I thought – at least one blog post a month won’t be difficult, right?
Right.
Then in February, right before I was scheduled to speak at eTail West, I get an ominous email from Google saying my blog is spewing malware. I immediately checked and was convinced the email was legit. Oh crap. Later Google would complain about many more sites I host, here’s an example email:
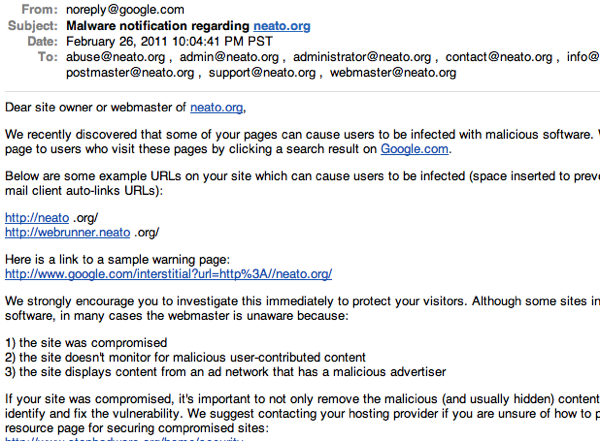
I host a number of sites (including some blogs, a mail server, a personal photo gallery, two commercial sites and a non-profit group) and all of them were compromised. So I disabled all the web sites until I returned from eTail. When I got back home, I cleaned and rebuilt each site one-by-one. During the rebuilds, sites were getting re-infected, and it was difficult to find the attack vector. The web wasn’t any help, except that I got a good appreciation for some of the old security issues in WordPress and its plugins – none of which I was experiencing.
It turns out that while bobpage.net was up-to-date with its software, another locally-hosted site was not, and got compromised. The attack granted access to the local file system, so every web site I hosted got infected. Nice. Once I installed some hand-rolled logging software I saw how quickly a site would get hit, and then infect everything else.
Finally I learned enough to understand this particular attack, and I installed various intrusion detection, firewall and logging packages, just in case, and turned on sites one-by-one until I was satisfied I had everything back under control. The whole thing probably took me two weeks to fix, since I couldn’t just drop everything else I was doing. But it did consume most of an entire weekend.
As to what the malware did, I never really looked. As long as it was gone I was satisfied.
Back in the day I ran all my own machines & software, built around FreeBSD and Linux. One day I decided there were better things to do than to continually monitor every mail list and patch my system software. So I switched my machines to Mac and went to outsourced hosting. That doesn’t solve everything but it did lower the administrative burden, because I was putting my faith in others who claimed they were up to the task. But I couldn’t fully give up everything, so I went with a self-administered version of WordPress instead of using the hosting and software available at wordpress.com. As a result, a slip-up in my software patching caused me days of hassle.
That was late February – early March. For now, I’m still using my own hosted version of WordPress, because I keep telling myself it gives me lots of flexibility should I want/ need it. Today I installed the latest patches, checked my logs, and decided it was safe to blog again (for some definition of ‘safe’). I’m not a big fan of blogging about blogging, but the larger story is that no matter how remote and isolated you think you are, you’re running buggy software at the end of some IP address. The scanners will find you, and the scammers will take advantage if they are able. Whether or not you care depends on how much control/flexibility you want. But I guess with great flexibility comes great responsibility, or something like that.
 I’ve been dorking with
I’ve been dorking with 

